1. Introduction
Hashcat is a powerful password cracking tool used by cybersecurity professionals and ethical hackers. In this article, we will examine what Hashcat is, how it works, and how it is used in the cybersecurity field.
1.1. What is a Hash?
A hash is a mathematical operation that produces a unique string of fixed length by subjecting a dataset to a formula determined by an algorithm. Essentially, the same input always produces the same hash value, but even a small input change results in a large hash change. This property ensures the uniqueness and reliability of the hash.
1.2. What is Hashcat?
Hashcat is open-source password cracking software. Its primary purpose is to crack cryptographically hashed passwords and detect security vulnerabilities. Hashcat offers the ability to crack various encryption methods by supporting different hash algorithms. Hashcat has a wide application area supporting popular hash algorithms like MD5, SHA-1, and SHA-256.
2. Working Principle
Hashcat performs password cracking operations using various attack modes. It attempts to crack hash values using methods such as Brute Forcing (Brute Force Attack), Dictionary Attacks, and Combination Attacks. Thanks to its flexible usage, it adapts to different scenarios.
2.1. Hashcat Installation
2.1.1. Windows
To install Hashcat, all you need to do is download the Windows version from Hashcat official website and extract the compressed file to a folder. Then, by opening Command Prompt or PowerShell, you can check if Hashcat is successfully installed and verify the version using the following command.
hashcat --version2.1.2. MacOS
First, the Homebrew package manager should be downloaded by opening the terminal. Then Hashcat should be installed using the following command.
brew install hashcatTo check if Hashcat is properly installed and working, the following command can be used.
hashcat --version2.1.3. Linux
First, system packages should be updated:
sudo apt-get update
sudo apt-get upgradeThe following command should be used to download Hashcat.
sudo apt-get install hashcatThe following command should be used to check if Hashcat is successfully installed and for version control.
hashcat --version2.2. Hashcat and Password Cracking Techniques
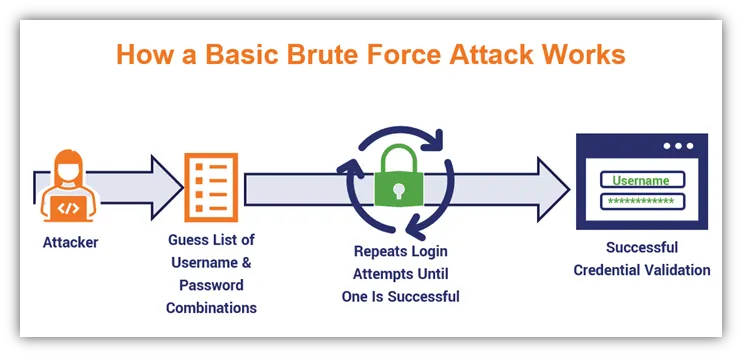
2.2.1. Brute Force
The Brute Force password cracking approach, also known as Brute Force Attack, is technically simple but has disadvantages. It attempts to crack passwords by trying all possible combinations. This method can be effective for small and simple passwords, but can be very time-consuming for large and complex passwords. For example; for a 5-digit password consisting of letters in the a-z range and numbers in the 0-9 range with Turkish special characters removed, the total number of possibilities to be tested is:
a-z = 26 characters
0-9 = 10 characters
(26+10) = 60,466,176
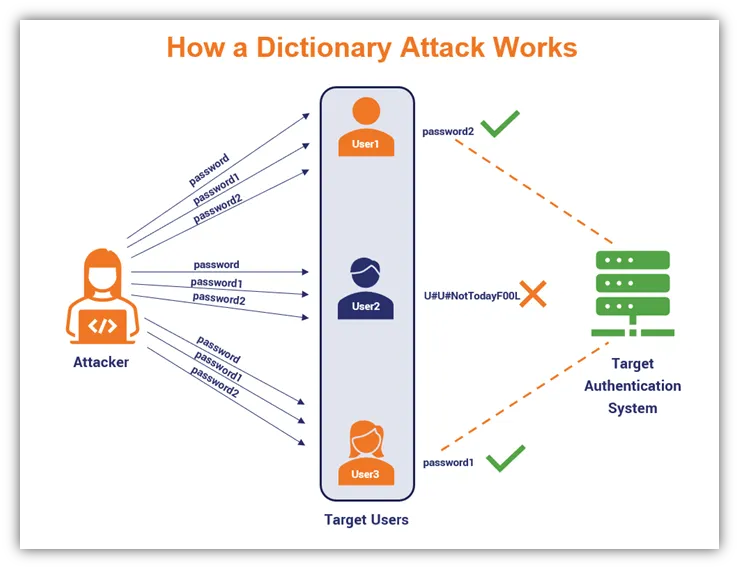
2.2.2. Dictionary Attacks
Dictionary Attacks, translated as dictionary attacks, attempt to crack passwords by trying them using a pre-prepared word file. Dictionary Attacks is an effective method for situations where users tend to choose common passwords. To increase the method success rate; combinations of contents in the word file should be made with each other.
Example Dictionary Attack:
Step 1: Creating Word File - The individual creates a dictionary file appropriate to the target structure and language. This file contains common passwords, words, brand names, usernames, and similar elements.
Step 2: Launching the Attack - Hashcat launches the dictionary attack for each hash value in the target system hashed password database using the created dictionary file.
Step 3: Cracking Passwords - Hashcat attempts to crack the hash value by trying each element in the dictionary file. When a matching value is found, the individual has successfully cracked the password.
Prevention and Protection: To protect against dictionary attacks, it is important to use strong and complex passwords. Additionally, measures such as updating systems password policies, adding automatic account lockout mechanisms, and limiting attacks with firewalls can be taken.
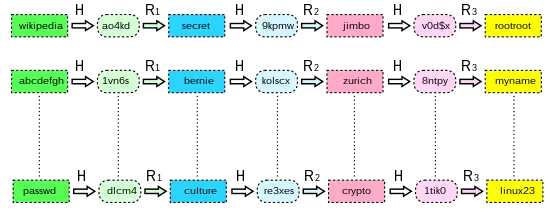
2.2.3. Rainbow Tables
It shows similarity to Dictionary Attacks by keeping a list of words with known hash equivalents. The difference is that no hashing operation is performed in this attack type. Since the most important point of hash cracking work is to reach results in a short time, the hash to be cracked is compared with hashes kept in Rainbow tables. If a match occurs, which word corresponds to this hash is checked from the Rainbow tables. Since no hashing operation is performed in this way, the process is much faster.
Example Rainbow Tables Attack:
Step 1: Preparing Rainbow Tables - The individual pre-calculates the rainbow tables database to cover a wide search space. This table contains hash values and corresponding passwords.
Step 2: Finding Target Hash Value - The target hash value is searched within the pre-prepared rainbow tables. If a matching value is found, this means the target password has been found.
Step 3: Cracking Password - The password found for the matching hash value is the target system password. The individual can log into the system using this password.
Prevention and Protection: To protect against rainbow tables attacks, it is important to use strong and complex passwords. Additionally, the salting method that makes hash values current and unique can also be used.
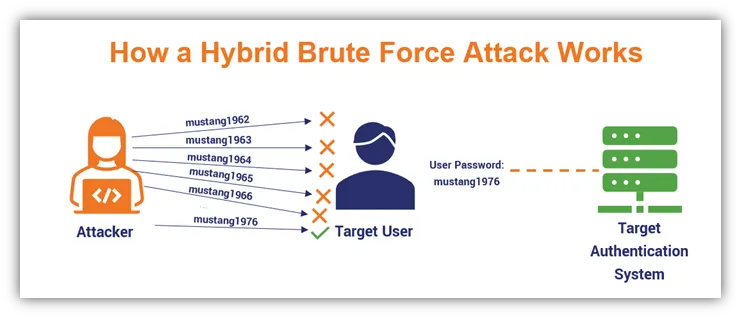
2.2.4. Hybrid Attacks
Hybrid Attacks is a password cracking technique where two or more strategies are combined. It is generally a combination of Dictionary and Brute Force attacks. This attack type, which combines different password cracking strategies, attempts to crack encryption algorithms by using multiple strategies simultaneously. It is a hash cracking technique that can succeed against the salt application we mentioned in Rainbow Tables.
Example Hybrid Attack:
Step 1: Determining Character Combinations - The individual determines character combinations appropriate to the target system password complexity. For example, combinations of uppercase, lowercase, numbers, and special characters.
Step 2: Determining Attack Modes - By determining different attack modes, combines brute force attack, dictionary attack, and similar strategies.
Step 3: Launching Hybrid Attack - Using Hashcat or a similar tool, launches the password cracking process using determined character combinations and attack modes. For example, first tries simple combinations then switches to dictionary attack.
Step 4: Evaluating Results - Evaluates hybrid attack results and cracks the password by recording successful combinations.
Prevention and Protection: To protect against hybrid attacks, it is important to use strong and complex passwords. Additionally, measures can be taken by adding automatic account lockout mechanisms and updating password policies.
2.2.5. Mask Attacks
Mask attacks is a password cracking strategy that attempts to guess passwords based on a specific pattern. This pattern can include a specific character set and specific positions. Mask attacks offers a more optimized method compared to brute force attacks. To give a small example of the working logic, many people use numbers toward the end digits of their password or their password first character starts with a capital letter. Mask Attacks performs hash cracking operations by utilizing patterns we can specify specifically.
?l = abcdefghijklmnopqrstuvwxyz
?u = ABCDEFGHIJKLMNOPQRSTUVWXYZ
?d = 0123456789
?h = 0123456789abcdef
?H = 0123456789ABCDEF
?s = space!"#$%&'()*+,-./:;<=>?@[]^_`{|}~
?a = ?l?u?d?s
?b = 0x00-0xff
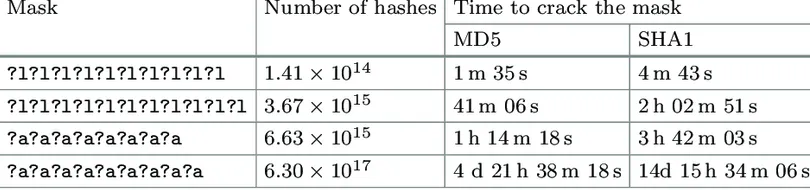
So which method should be chosen? If you want to crack as many hashes as possible simultaneously, Hybrid and Mask attacks will show more success. In cracking work targeting a single hash, choosing Dictionary or Rainbow increases the possibility of reaching results faster.
3. Hashcat Key Features
- Support for various hash algorithms (MD5, SHA-1, SHA-256, etc.).
- Flexible usage opportunity with different attack modes.
- Ability to run on GPU and CPU, providing high performance.
- Ability to perform effective dictionary attacks by creating password combinations.
- Provides high performance with parallel computing capabilities and fast hash solving.
- Offers users the opportunity to define and apply their own custom rules.
- Demonstrates effective performance in large databases thanks to low memory usage and memory optimization.
4. Security Testing and Hashcat
Hashcat helps in detecting weak passwords in systems and identifying security vulnerabilities by being used in security testing. This allows organizations to evaluate their cybersecurity and enables early detection of potential risks. However, it is important that such tools are used only within legal and ethical boundaries.
5. Legal and Ethical Responsibilities
Like every powerful tool, Hashcat must also be used within legal and ethical boundaries. Illegal and unethical uses must be avoided. Proper use of Hashcat plays an important role in detecting security vulnerabilities and strengthening system defenses.

5.1. Legal Responsibilities
5.1.1. Authority and Permissions
Password cracking operations with Hashcat or similar tools should only be performed by the system owner or persons with necessary permissions. Password cracking operations performed without legal permission can constitute a crime.
5.1.2. Compliance with Corporate and Country Laws
Use of Hashcat must comply with corporate policies and country laws. In some countries, certain security tests may be subject to strict regulations, so users should pay attention to local legal regulations.
5.1.3. Plagiarism and Data Theft
Unauthorized use of information obtained during use of Hashcat can lead to data theft and unethical behavior. It is important that obtained data is used only for security evaluation purposes.
5.2. Ethical Responsibilities
5.2.1. Moral and Ethical Principles
Hashcat users should adopt moral and ethical principles during password cracking operations. Users should only perform security tests within legal and ethical boundaries.
5.2.2. Permitted Tests and Information
Security tests performed with Hashcat or similar tools should be done with the knowledge and permission of the system owner. This includes an informed consent process and provides interactive feedback to users during tests.
5.2.3. Customer Relations and Trust
Security testing professionals or ethical hackers should be transparent in client relationships and take care to preserve the confidentiality of obtained information.
5.3. Prevention and Protection
5.3.1. Legal Consultation
Users should receive legal consultation before using Hashcat or similar tools. This helps users ensure compliance with local legal regulations.
5.3.2. Permission Documents and Contracts
Security testing professionals should act in accordance with the legal framework by determining the scope and boundaries of tests through a permission document or contract signed with their clients.
5.3.3. Informative Training
Security testing professionals should provide informative content to clients and users explaining the purpose and process of security tests.
6. Hashcat Future
In an era when cyber threats are constantly evolving, development and updating of tools like Hashcat is important. Future versions of Hashcat can offer capabilities to crack more complex hash algorithms and more effective strategies against new security challenges.
In the future, Hashcat evolution will depend on another series of factors. Primarily, with the emergence of new security standards and hash algorithms, Hashcat is expected to support these algorithms. Additionally, performance improvements in Hashcat can be experienced with evolving GPU and parallel processing technologies.
User-friendly interface and comprehensive documentation improvements can contribute to Hashcat adoption by a wider user audience. Developments in security and compliance issues can enable Hashcat to become a more effective tool for security professionals.
Additionally, thanks to community contributions and its open-source structure, Hashcat can better respond to users needs. However, the importance of legal and ethical responsibilities expected from the software users is a fundamental element shaping Hashcat future. Users should continue to support developments in the cybersecurity field by using this powerful tool within legal and ethical boundaries.
References
- Hashcat Advanced Password Cracking Tool
- Hashcat - Wikipedia
- What is Hashing?
- Hash Nedir?
- Hashcat Nedir?
- Install Hashcat on Windows
- Hashcat on macOS
- Install Hashcat on Kali Linux
- Hashcat Kullanımı
- Brute Force Attack Nedir?
- Brute Force Attack Definition
- Rainbow Tables: A Path to Password Gold
- Rainbow Table Attack
- Rainbow Table - Wikipedia
- Hybrid Password Attacks
- What is a Hybrid Attack?
- Time of Mask Attack for MD5 and SHA1
- What is Hashcat?
- Cybersecurity Laws and Regulations
- Siber Güvenlik Nedir?